A Zoo of Security Notions for FHE
April 18, 2026 · 4 min read
As a PhD student in cryptography, security is - in theory - the main goal. In practice, day-to-day FHE research often looks more like high-performance computing: optimizing NTTs, finding algorithmic tricks to make some operations cheaper, or shaving off milliseconds from bootstrapping.
It is easy to lose sight of what “secure” actually means for FHE. And that question is surprisingly subtle.
Why FHE security is subtle
FHE inherits the usual IND-CPA goal from public-key encryption, but the structure of lattice-based schemes opens doors that classical encryption keeps closed:
- Ciphertext malleability. Homomorphic operations require the ability to transform ciphertexts into other valid ciphertexts. This is a defining feature of FHE, but it is fundamentally at odds with CCA-style security.
- Inherent noise. Every FHE ciphertext carries a noise budget. Whether a decryption succeeds or fails can itself leak information, and reactive adversaries can exploit it.
- Approximate computation. Schemes like CKKS return approximate results: the decrypted plaintext depends on the internal noise distribution, which in turn depends on adversarially-chosen messages.
These observations have produced a long line of work proposing security notions tailored to FHE: CPAD, sCPAD, vCCA, vCCAD, funcCPA, CCA1.5, CCVA1/2, gCCA, RCCA, HCCA, IV-CCA, SA, and more. The relative strength of these notions is rarely obvious at first glance.
An interactive taxonomy
To make this landscape easier to navigate, I built securitynotionszoo.com - an interactive taxonomy of cryptographic security notions for FHE.
Each notion in the zoo comes with:
- a formal definition of the security game,
- the papers that introduced or refined it,
- the implications it participates in (what it implies, what implies it), and
- tags and flavor annotations (indistinguishability vs. key recovery, with or without decryption oracles, etc.).
Relation map: who implies whom
The home page renders a graph where each arrow reads “A implies B” - a scheme secure in the sense of A is (usually strictly) secure in the sense of B.
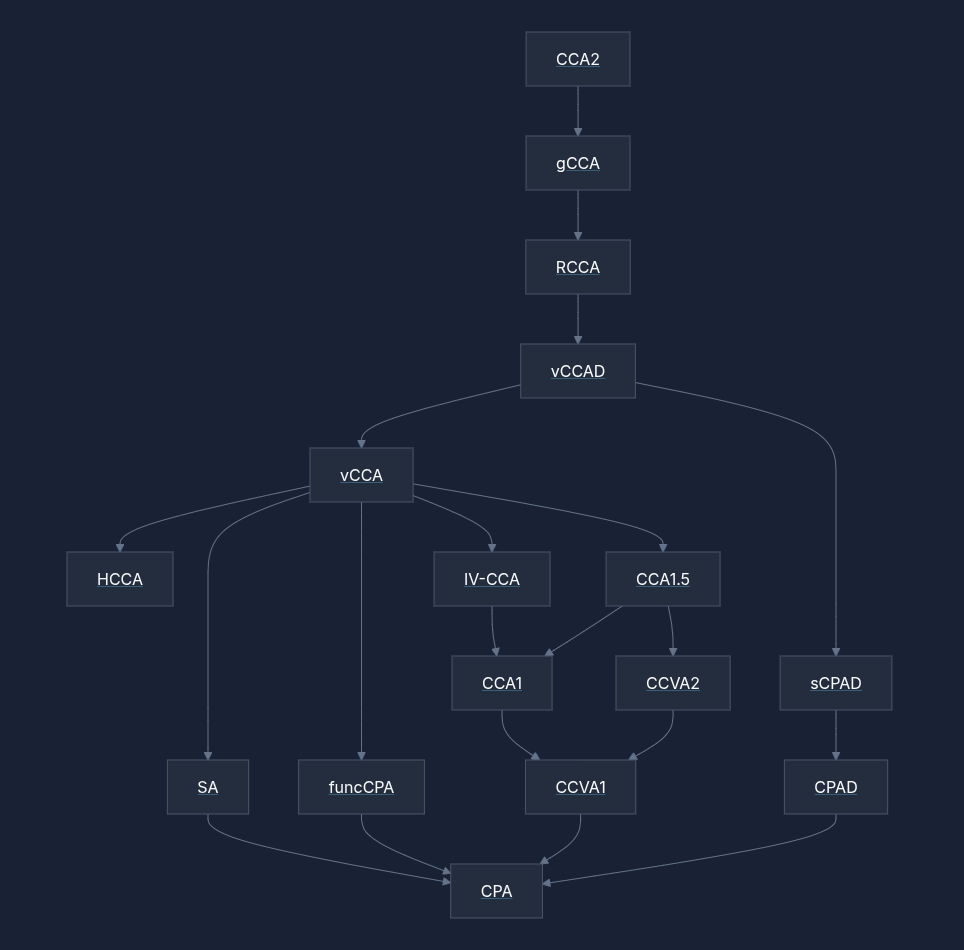
Trying to understand what CPAD means, or whether vCCAD is stronger than funcCPA? One click on the graph takes you to the full definition and references.
Transform map: labelled routes between notions
Implication on its own is a coarse picture - it tells you “this is stronger than that”, but not how to get from one to the other. The transform map answers the how: each arrow is a published transform that lifts a scheme from a weaker notion to a stronger one, labelled with the construction, the paper that introduced it, and the assumptions it relies on.
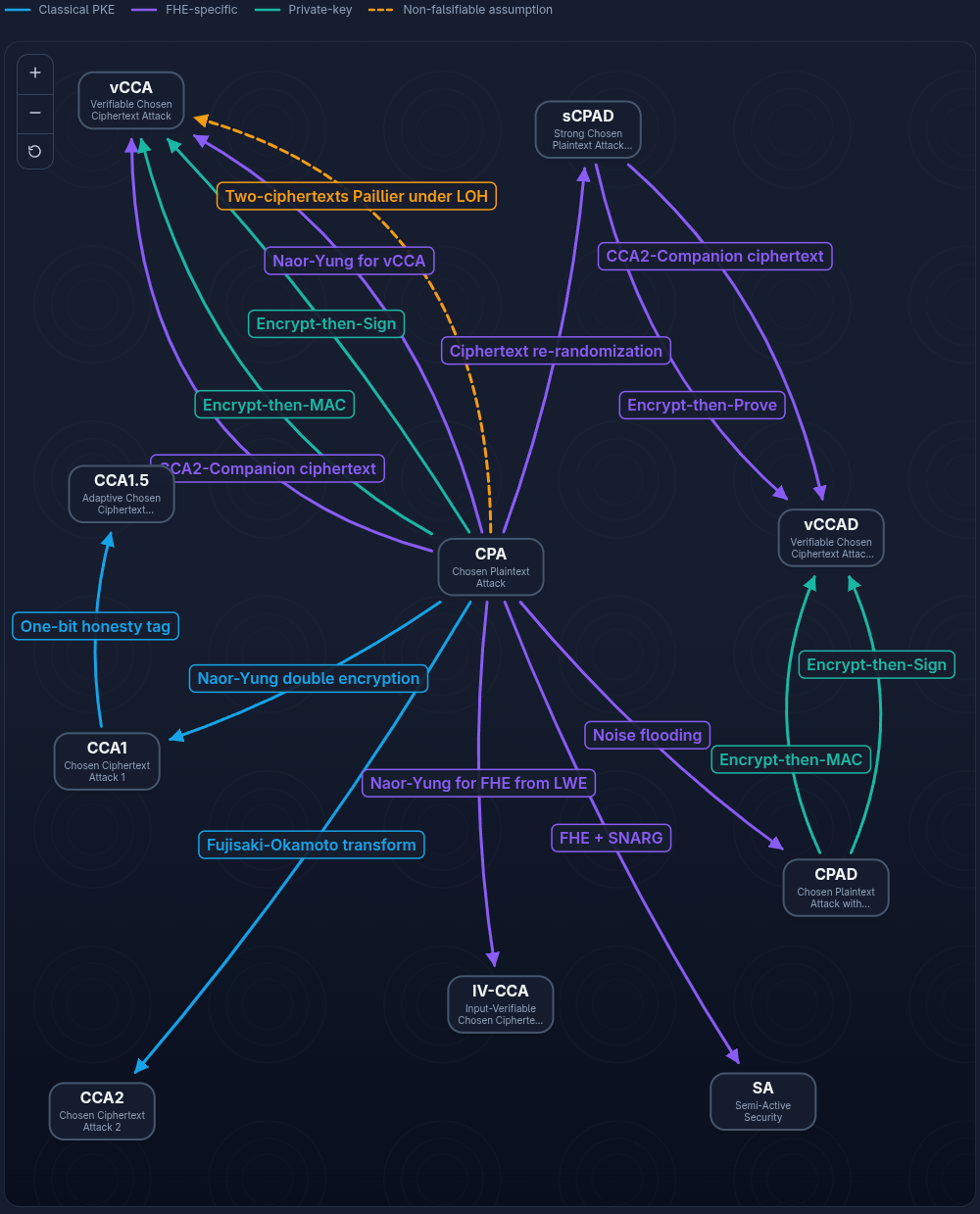
Arrows are colour-coded by setting (classical PKE, FHE-specific, private-key, non-falsifiable assumption), and tapping one opens the details of the transform.
Learning material
The zoo is not only a reference - it also ships beginner-friendly material for readers coming from outside provable security.
- A security primer walks through the vocabulary every definition in the zoo assumes: PPT adversaries, negligible functions, game-based definitions, reductions, and game hopping.
- A flavors page compares the sub-games (IND, KR, and others) that can be plugged into the same attacker-capability skeleton, making explicit the
XXX-YYYnaming convention used throughout the literature.
Together, these turn the zoo from a catalogue into a short self-study path.
Games
Browsing definitions is one thing; checking you actually know them is another. The games section offers small interactive exercises:
- Quiz - multiple-choice questions on acronyms, implications, and definitions.
- Recreate the graph - draw every implication arrow from scratch, at three difficulty levels (CPA/CCA ladder, common FHE extensions, full taxonomy).
- Build the adversary - for each notion, pick the oracles and capabilities that define its adversary’s game: pre-challenge oracle, post-challenge oracle, and encryption randomness.
They are short and oddly addictive.
Open source
Both the site and its content are open source.
- Code: github.com/jdumezy/securitynotionszoo
- Live site: securitynotionszoo.com
Adding a new notion is a single Markdown file under src/content/notions/ with a small Zod schema (title, acronym, description, tags, introducing papers, implications).
If you spot a missing notion, an outdated reference, or an error in one of the implications, issues and pull requests are very welcome.
Thanks to Marc Renard for contributing to this first version.